Use cryptography; don’t learn it
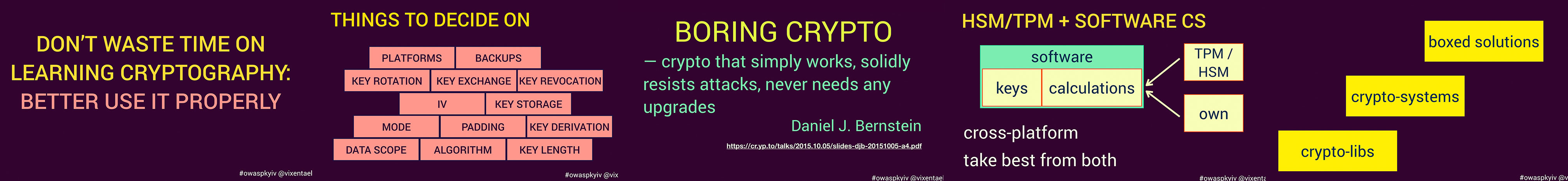
We’ll talk about “boring crypto”: why developers shouldn’t spend time learning all the details of crypto-algorithms (or invent new ones). How to avoid typical crypto-mistakes when all you need is to protect data at rest or in motion. There are enough ready-to-use cryptographic libraries and tools for everyone.
Points we cover
- The typical engineering workflow “we should protect the data, what shall we do”, and possible mistakes.
- What is “boring crypto”, what do we want from using crypto-products.
- Possible solutions: HSM / TPM / software crypto.
- How to select appropriate software crypto: libs, systems, containers.
- We want crypto to be similar to the Edison lamp: controllable and boring system.
Watch 📺
Click to read slides.Presented at ✨
OWASP Chapters All Day Online, June 2020
Swift and Fika Stockholm, Sweden, 10 September 2018
Devexperience.ro Iasi, Romania, 23 April 2018
OWASP Kyiv Meetup Winter 17 Kyiv, Ukraine, 2 December 2017